What Public Trust Actually Is and What It Is Not?
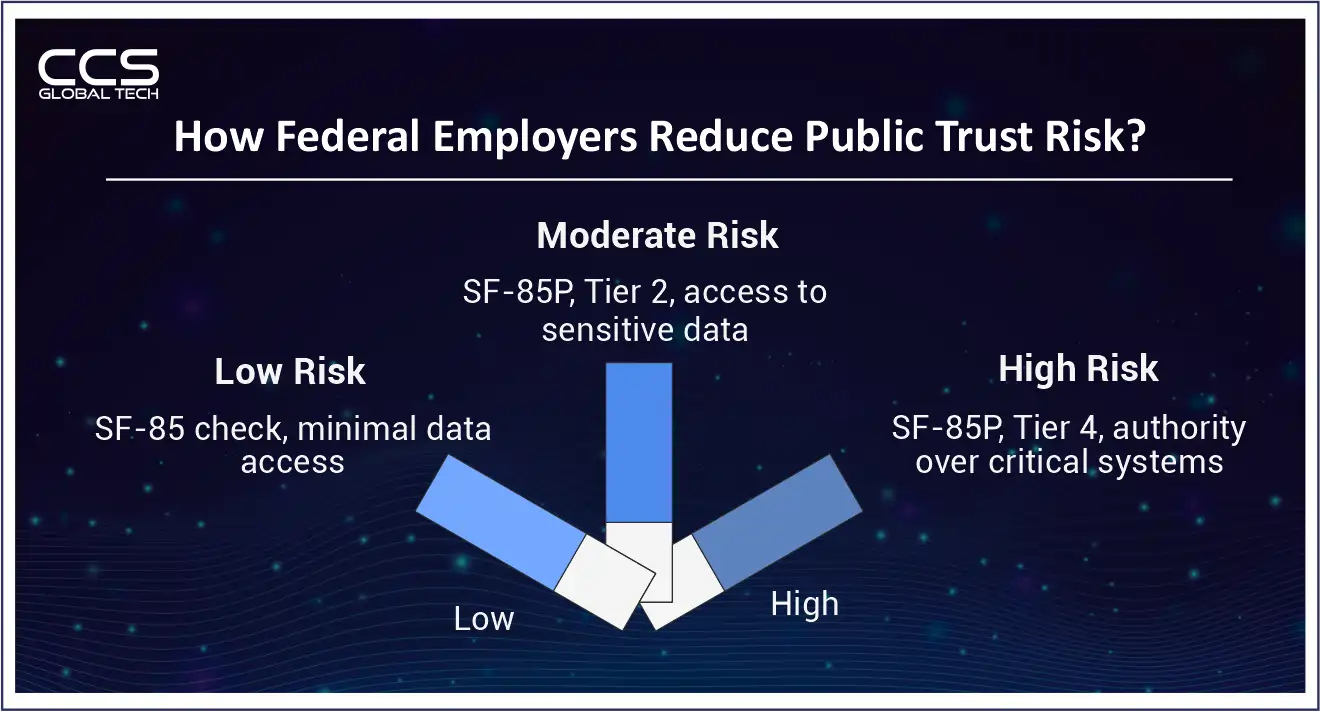
- Low Risk (non-Public Trust): Entry-level or administrative roles with minimal access to sensitive data or systems. Background investigation conducted using SF-85.
- Moderate Risk Public Trust (MRPT): Roles involving program administration, access to sensitive but unclassified records, or responsibility over government databases. Requires SF-85P and a Tier 2 investigation.
- High Risk Public Trust (HRPT): Positions with major decision-making authority, oversight of critical IT systems, control of significant financial resources, or access to large volumes of personally identifiable information. Requires SF-85P and a Tier 4 investigation.
The Forms Landscape in 2026: What Has Changed and What Is Coming?
The Processing Reality: Timelines, Backlogs, and What to Plan For
A Federal Contractor’s Hard Lesson in Position Risk Designation
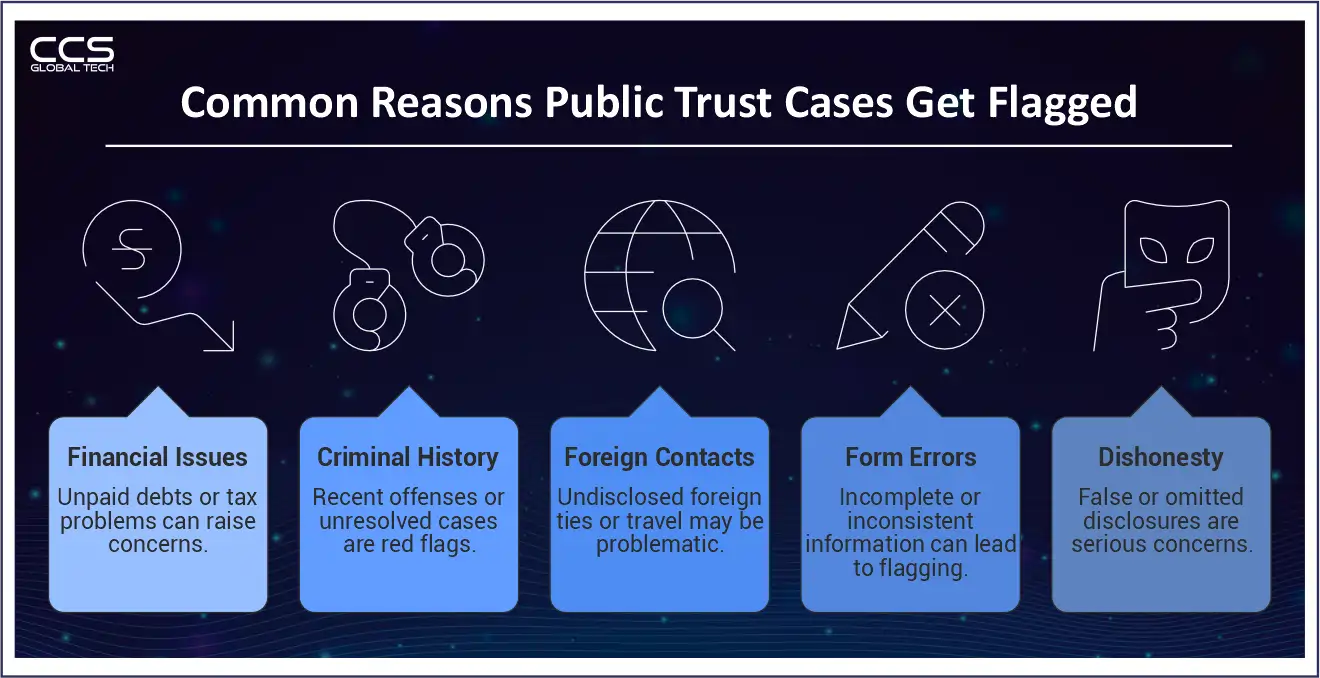
Red Flags: What Gets Cases Flagged, Delayed, or Denied
Financial Issues
- Significant outstanding delinquent debt (especially to the federal government).
- Unexplained gaps between reported income and lifestyle indicators.
- Multiple bankruptcies within a short period without clear mitigating circumstances.
- Failure to file required tax returns.
Criminal History
- Felony convictions, particularly those involving fraud, theft, or violent offenses.
- Recent drug-related offenses.
- Domestic violence convictions (which can also affect firearms eligibility in federal facilities).
- Outstanding warrants or unresolved charges at the time of application.
Foreign Influence and Contacts
- Close relatives who are foreign nationals in countries of concern.
- Significant financial interests or business relationships in foreign countries.
- Failure to report foreign travel on the questionnaire.
- Prior foreign government employment not disclosed.
The Single Biggest Red Flag: Dishonesty on the Form
The New Normal: Continuous Vetting and What It Means for Current Employees
Getting Ahead of the Process Is the Only Strategy That Works
FAQs
Q1. How long does a Public Trust clearance investigation take in 2026?
A – Processing times vary based on the investigation tier and case complexity. Moderate Risk Public Trust investigations typically take three to five months for straightforward cases, while High Risk Public Trust investigations can take six months or longer.
Q2. What causes delays in a Public Trust background investigation?
A: Delays usually occur due to incomplete forms, missing employment history, undisclosed financial issues, slow responses from references, or incorrect position risk designation that requires resubmitting investigation paperwork.
Q3. What financial issues can raise red flags during a Public Trust investigation?
A: Investigators review delinquent debts, unpaid federal taxes, repeated bankruptcies, and unexplained financial discrepancies. The focus is on patterns that may indicate financial irresponsibility or vulnerability to external pressure.
Q4. Can someone with a criminal record still obtain a Public Trust determination?
A: Yes. A criminal record does not automatically disqualify an applicant. Adjudicators evaluate the seriousness of the offense, how recent it was, whether there is a pattern of behavior, and evidence of rehabilitation.
Q5. What happens if information is omitted on the SF-85P form?
A: Omitting required information can trigger additional investigation and may lead to an unfavorable determination. Investigators often treat omissions as seriously as intentional misrepresentation.
Q6. What is continuous vetting and how does it affect Public Trust employees?
A: Continuous vetting replaces periodic reinvestigations with ongoing automated monitoring of criminal records, financial indicators, and other relevant databases. Alerts can trigger targeted reviews when new issues appear.
Q7. What is the Personnel Vetting Questionnaire (PVQ)?
A: The Personnel Vetting Questionnaire is a new modular background investigation form being developed under the Trusted Workforce 2.0 initiative. It will eventually replace the SF-85, SF-85P, SF-85P-S, and SF-86.
Q8. Can a candidate start work before Public Trust clearance is finalized?
A: In some cases candidates may begin work under an interim determination or with limited system access, depending on agency policy and contract requirements.
Q9. What is the most common mistake organizations make with Public Trust hiring?
A: Incorrect position risk designation is a common issue. When a role is classified at the wrong risk level, the investigation often has to restart under the correct tier, which can delay onboarding.
Q10. How can federal contractors reduce delays in Public Trust investigations?
A: Contractors can reduce delays by designating position risk levels correctly, preparing candidates before forms are submitted, verifying form accuracy, and coordinating closely with security officers during the investigation process.





